USB Forensics unlocks the mysteries of what happens from the moment you plug in a USB device until you disconnect it. USB Mass Storage devices are the focus of the course. In addition to leveraging Linux and free tools to learn how USB devices work, you will learn how to build USB Mass Storage device pocket forensic duplicators, write blockers, and impersonators.
– Dr. Philip Polstra
Instructor, Linux Forensics and USB Forensics
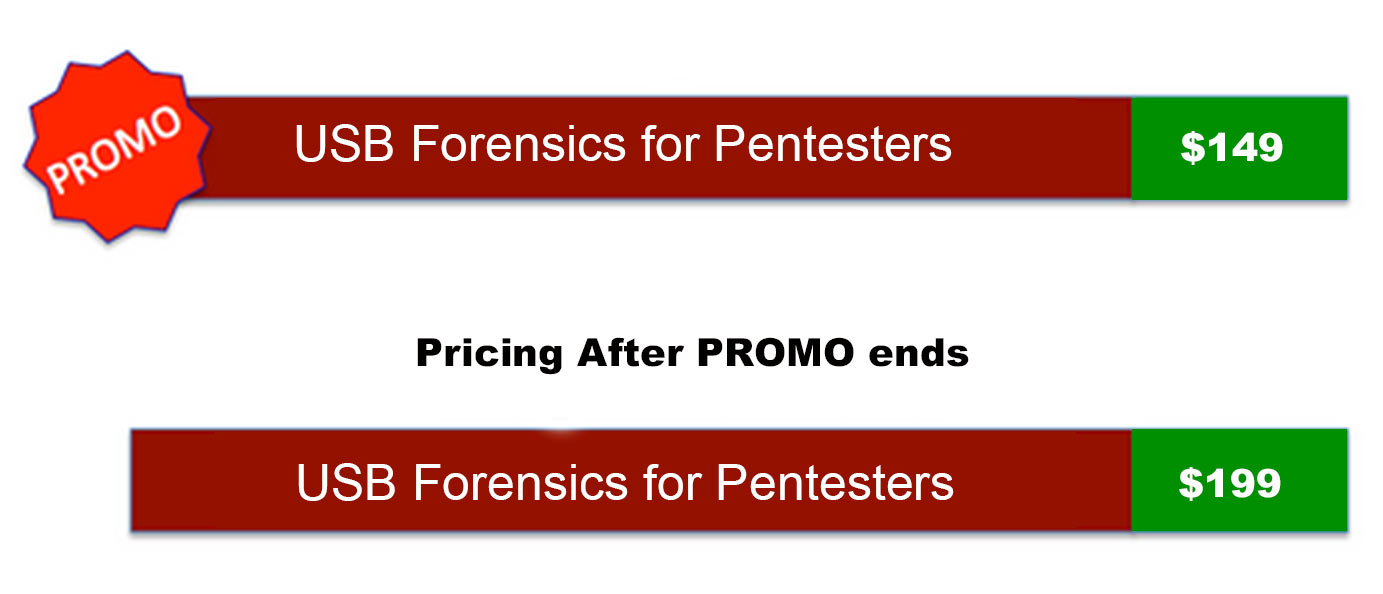
Question?Promotional Pricing – Enroll Now!
Only need the Course Videos? Get all our courses at just $39/month
1. What is the USB Forensics course about?
This course will cover USB in detail with an emphasis on understanding USB Mass Storage devices (also known as flash drives or thumb drives).By the end of this course students will know how to sniff USB traffic using open source tools, be able to write-block USB mass storage devices using software and microcontroller-based hardware, be able to impersonate other USB devices, and understand how to make forensic duplicates of USB mass storage devices. Along the way students will also learn how to use microcontrollers and Udev rules.
2. Course Syllabus
A non-exhaustive list of topics to be covered include:
- USB basics
- USB hardware
- USB versions
- Connection process
- USB classes
- HID
- Mass storage
- Others
- USB endpoints
- Interupt
- Bulk
- Isochronous
- Control
- Descriptors
- Device
- Interface
- Configuration
- Endpoint
- String
- Mass Storage Basics
- Presentation (SCSI hard drive)
- NAND flash limitations
- Communication
- Command Block Wrappers
- Data transport phase
- Command Status Wrappers
- Making forensic images and duplicates
- FTDI Vincullum II microcontroller
- Simple compact duplicator
- Reading sectors
- Main processing loops
- Hardware implementation
- Programming the hardware
- Improving performance
- More user friendly duplicator
- Adding an LCD screen
- USB Write blocking
- Motivation
- Software write blocker
- Hardware write blocker
- Mitigation of BadUSB and similar threats
- USB Impersonation
- Motivation
- High level design
- Timers
- Descriptor request handler
- GPIO (buttons and displays)
- Software
- Hardware
- Buttons
- LEDs
- LCDs
- Leveraging Open Source
- Lsusb
- Understanding Linux USB busses
- Dmesg
- Sniffing USB traffic
- Usbmon
- WireShark
- Viewing descriptors in WireShark
- Dealing with Windows-only devices
- Using udev rules
3. Can I see some sample videos for the course?
The total duration of the course videos is a staggering 6+ HOURS of HD content. The course is fully hands-on and you will be spending most of the time doing exercises with the instructor.
The course starts from the very basics and slowly takes you to more complicated topics, making it ideal for self-paced learning. Below are a couple of sample videos from the course:
1. USB Forensics and Pentesting (Introduction)
2. USB Forensics – USB Descriptors Demo
3. USB Forensics: USB Mass Storage Descriptors and Endpoints
4. USB Forensics: USB HID Overview
5. USB Forensics: Challenge 2 Solution
Promotional Pricing – Enroll Now!
4. What do I get as a registered student?
A registered student will get the following:
- HD Download of Course Theory Videos
- HD Download of Course Exercise Videos
- PDF Slides of the full course
- All Code samples used in the course
- Mock Exam
- Certification Exam
- PDF copy of certificate if you pass the exam
Please note that there is no student forum associated with this low-priced course.
Promotional Pricing – Enroll Now!
5. What is the course duration? when does it start / stop ?
The USB Forensics course is completely self-paced, self-study course. There is no duration of the course or expiry period.
6. Student Testimonials from our existing Certifications
SecurityTube Certifications are currently taken by students from over 90+ countries around the world! Here is what our students have to say about us:

I found the SecurityTube Linux Assembly Expert course to be unique as it challenges the trainee to research and write implementations himself rather than just learning a book. This is also reflected by the exam which requires the user to go hands and which, in my opinion, tests the skills of the user a lot better than a multiple choice exam can. I also liked the fact there weren’t any time constraints on when to take the exam, which made it infinitely easier to plan in with regards to my job. The fact you also get a complete GDB course as an extra is a real bonus (Vivek wants to make sure you really know how to use your basic tools). The best part of the SLAE was the price, there are little other trainings of the same quality with the same price.
– Lucas Kauffman
IT Security Advisor
Ernst & Young

After having done my homework on reviewing numerous other online courses covering the subject matter that I wanted to study, I finally chose to settle on taking the SecurityTube Linux Assembly Expert course. I can now confidently state that I was very satisfied with my choice. I was not a novice assembly programmer going into the course, but given the level of confidence and clarity that Vivek had in teaching the material I am positive that even beginners would be able to follow along just fine. I myself feel like I have now gained a deeper appreciation for the subtle nuances of assembly programming in the information security field. My warmest thanks to Vivek and the staff at SecurityTube for all their detailed time spent on teaching this course.
– Thanesh Gopal
Software Engineer
Ottawa, Canada
The SecurityTube Linux Assembly Expert course is one of the few courses that I recommend to everyone I meet. Not only is it well put together and comprehensive, the materials are expansive without degrading quality. I’ve been writing shellcode for ten years now, and Vivek still managed to teach me ways of doing things I’d never thought of before. The SLAE course and certification require proof of knowledge that other courses miss, and anyone who has passed it has my utmost respect.
– Jason Spalding
Senior Systems and Security Engineer
Education, Government
7. Why Choose SecurityTube Certifications?

Our Certifications are taken by students from over 90+ countries and are Globally recognized. The Flags in the image to the left are countries from where our students belong. In addition, SecurityTube Certifications provide:
- High Quality Content at an Affordable Cost
- The most Comprehensive Course Coverage in the Industry
- Uses Open Content for Course Evaluation
- Concept Oriented, Practical Content rather than only Theory
Promotional Pricing – Enroll Now!
8. Course Instructor
Dr. Philip Polstra (Dr. Phil) has been involved with technology since an early age. He and one of his brothers cleaned out their savings to purchase a TI-99/4a computer in the early 80’s, much to the chagrin of his parents. He has been tinkering with computers and electronics ever since. Phil is an internationally recognized hardware hacker and information security expert. He has made repeat appearances at several of the top conferences worldwide. Here are just a few of the conferences he has spoken at: DEFCON (six times in four years), Blackhat, 44CON, GrrCON, BruCon, ForenSecure, SecTOR, c0c0n, Shakacon, B-sides Detroit, and B-sides Iowa. His work on developing small affordable hacking devices is documented in the book “Hacking and Penetration Testing with Low Power Devices”. He is also known for his work on USB hacking and forensics. Phil has published several articles on USB-related topics.
Phil is an internationally recognized hardware hacker and information security expert. He has made repeat appearances at several of the top conferences worldwide. Here are just a few of the conferences he has spoken at: DEFCON (six times in four years), Blackhat, 44CON, GrrCON, BruCon, ForenSecure, SecTOR, c0c0n, Shakacon, B-sides Detroit, and B-sides Iowa. His work on developing small affordable hacking devices is documented in the book “Hacking and Penetration Testing with Low Power Devices”. He is also known for his work on USB hacking and forensics. Phil has published several articles on USB-related topics.
Phil is an Associate Professor in the department of Math, Computer Science, and Statistics at Bloomsburg University of Pennsylvania where he teaches Digital Forensics. His current research focus is on developing ultra-low-power hacking hardware. Phil also performs security penetration tests and forensic investigations on a consulting basis. His book “Linux Forensics” is considered a must have by a number of people in the forensics and information security community.
In addition to in-person training, consulting, presenting at conferences, and running conference workshops, Phil has also produced hundreds of instructional videos. His video courses are available at PentesterAcademy.com, PluralSight, O’Reilly, udemy.com, and elsewhere.
When not teaching, Phil enjoys spending time with his family, tinkering with electronics, attending infosec conferences, experimenting with software defined radio (SDR) and various aviation activities. Phil is an accomplished aviator with a dozen ratings, all of which are current. Phil’s ratings include Commercial Pilot, Flight Instructor, Airframe and Powerplant Mechanic, Aircraft Inspector, and Avionics Technician. His flight hours are measured in the thousands and he has been known to build aircraft.
9. Course Enrollment and Payment
Buy now with Paypal!
10. Contact Us
We have compiled a FAQ below:
Click to Expand FAQ…
Please use the form below if you have any additional questions not answered by this page and we will get back to your ASAP: